Here are some images of the deployed application.
The view for a participant that is at the Yellow Belt Level
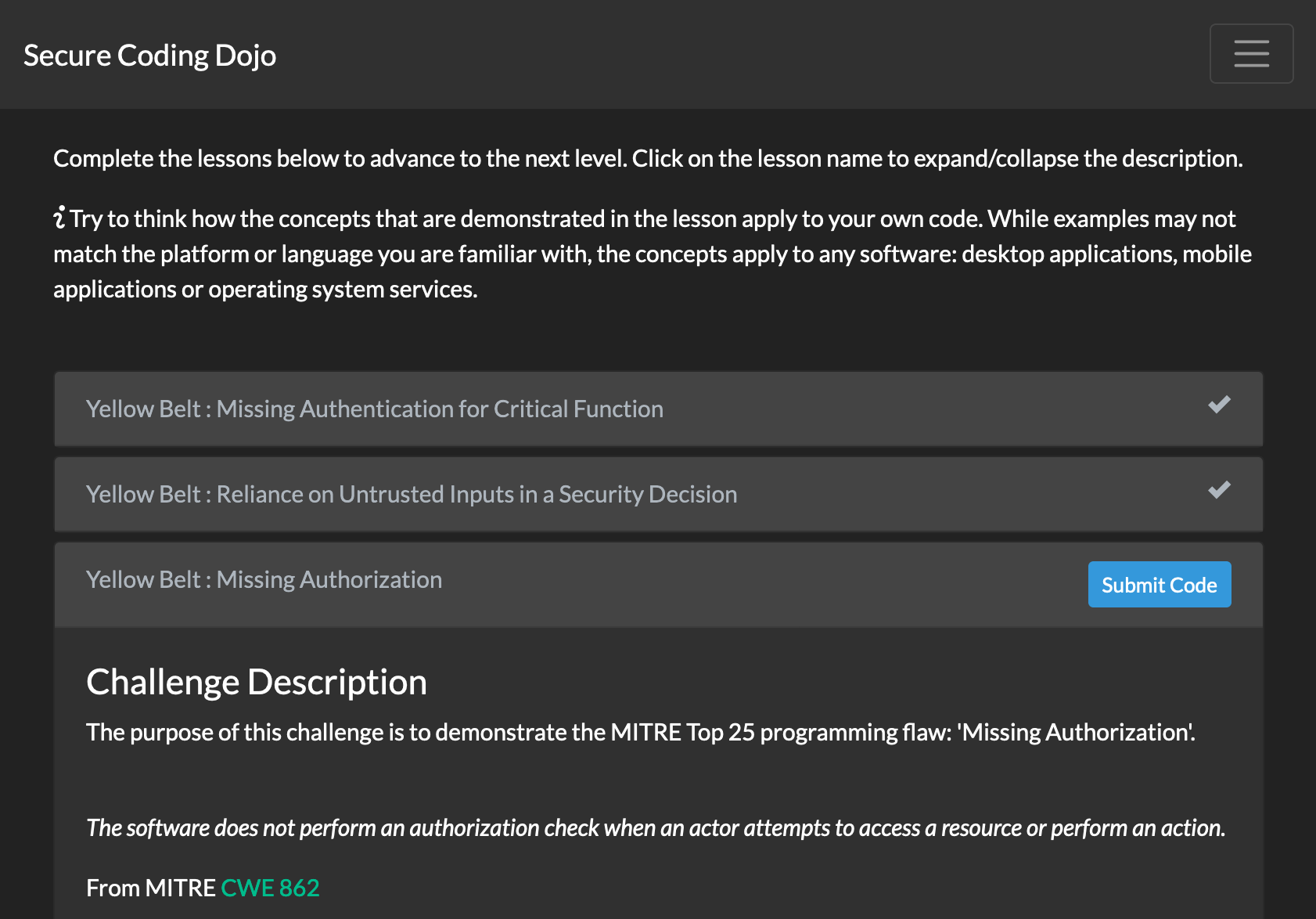
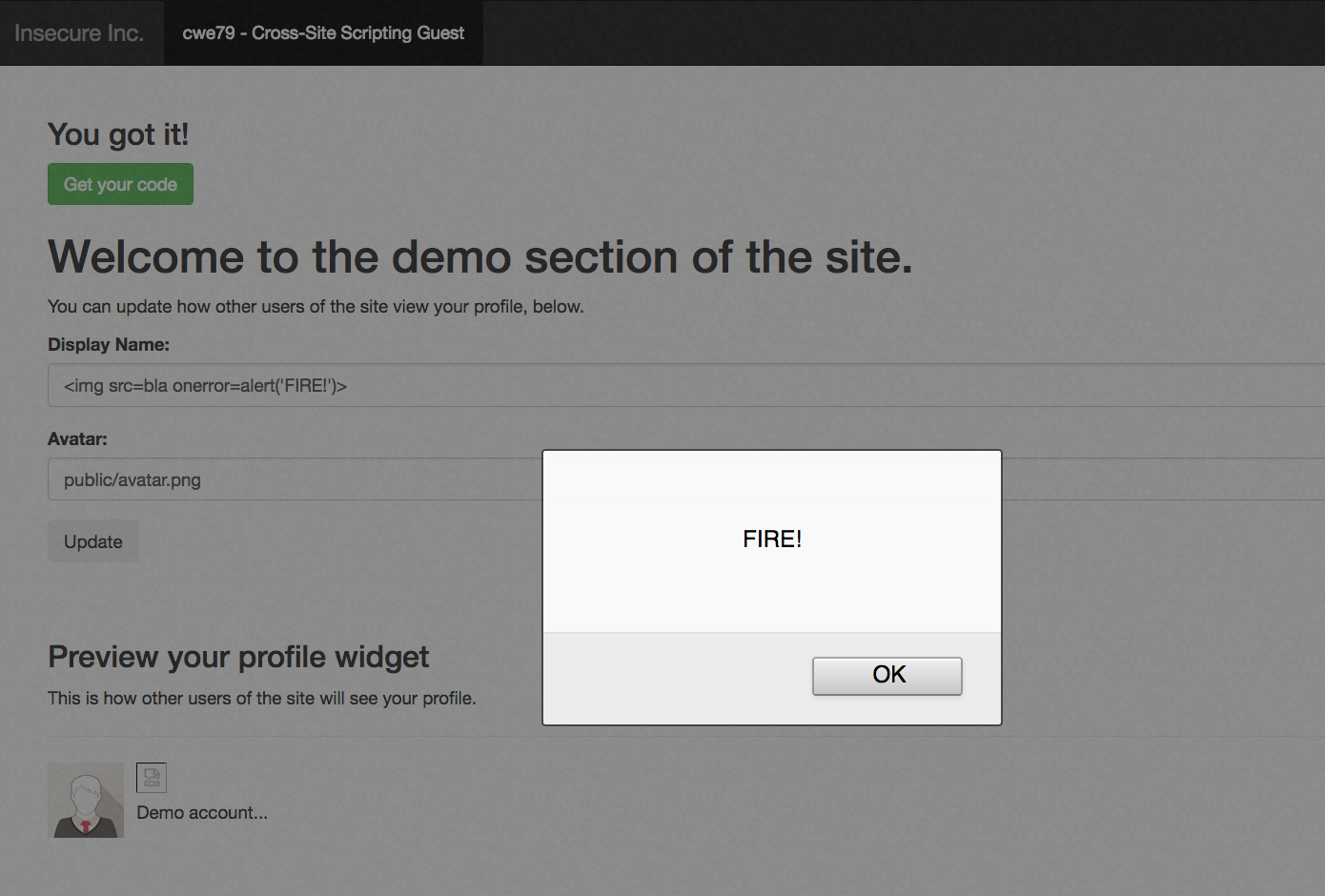
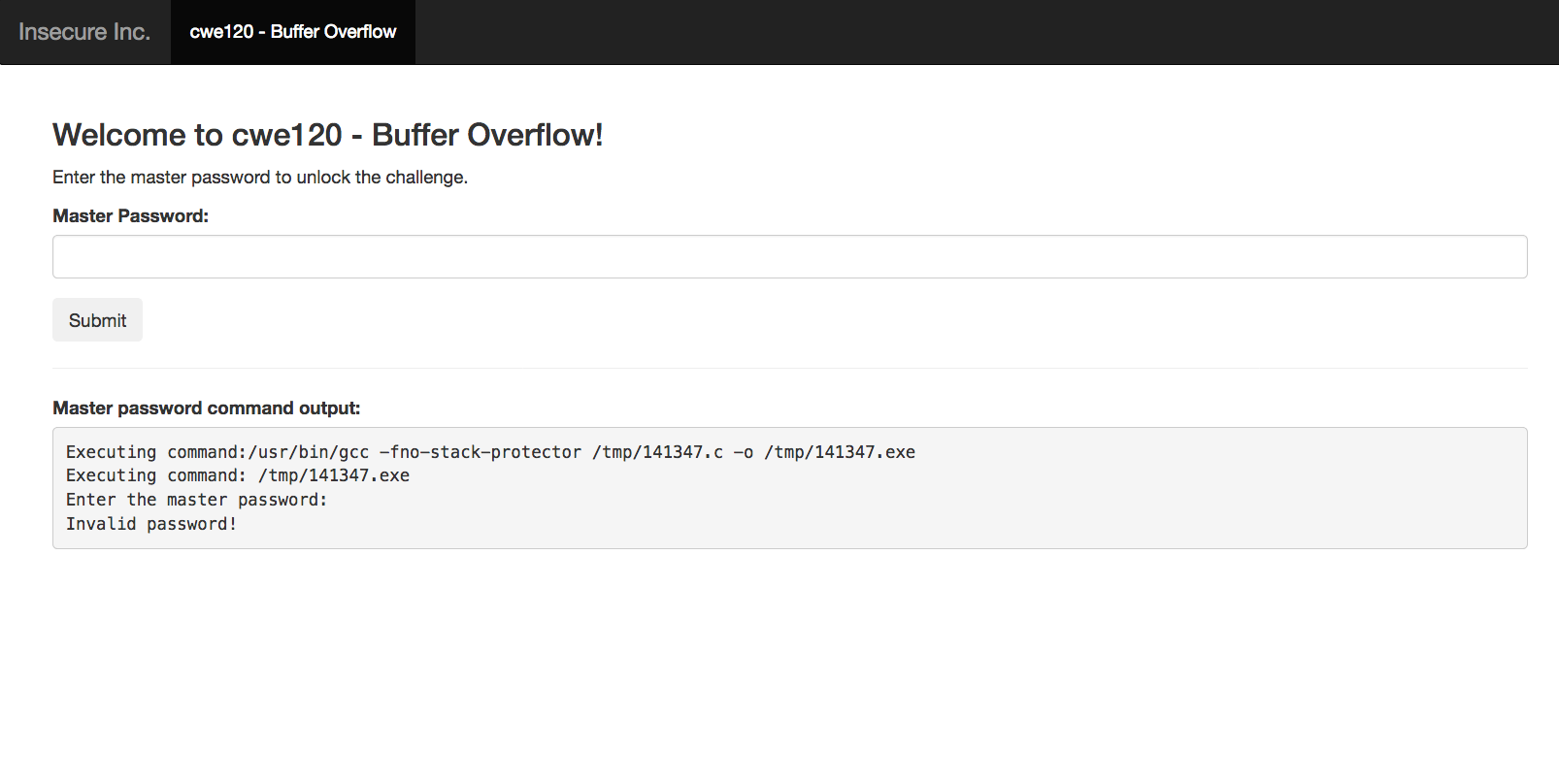
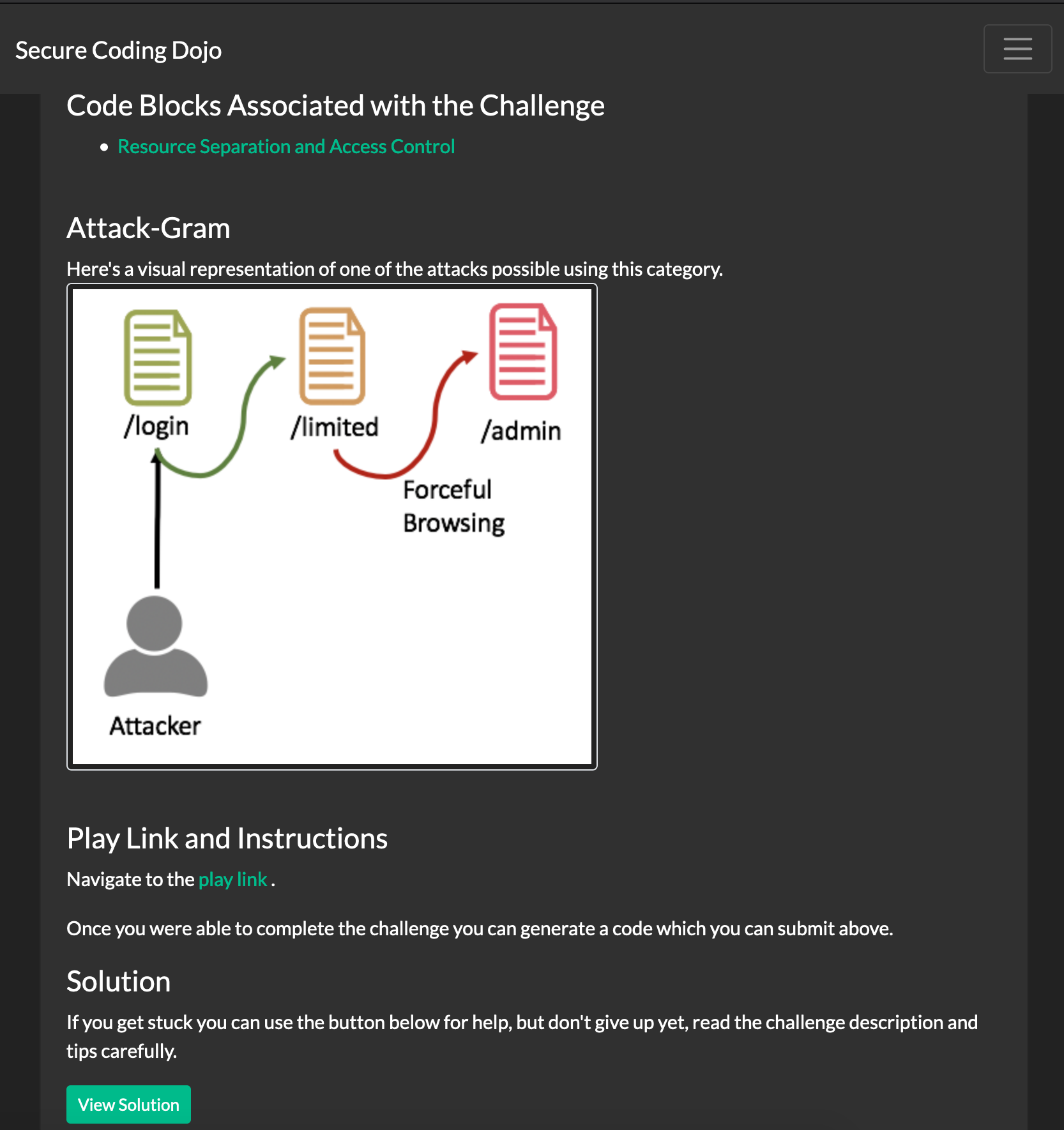
Each challenge contains details about the vulnerability being exploited.
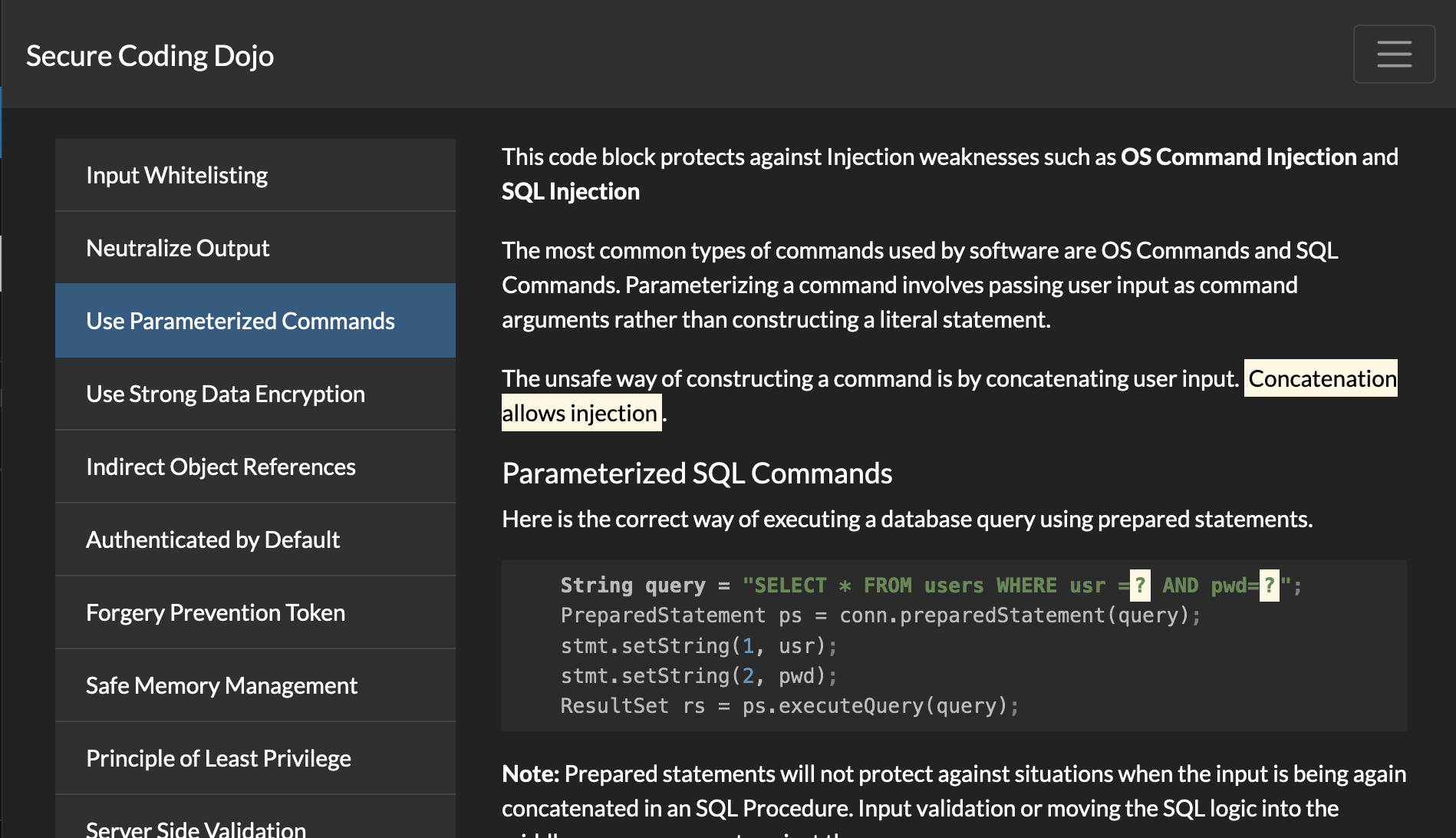
The page listing software defences that are used to prevent the issues
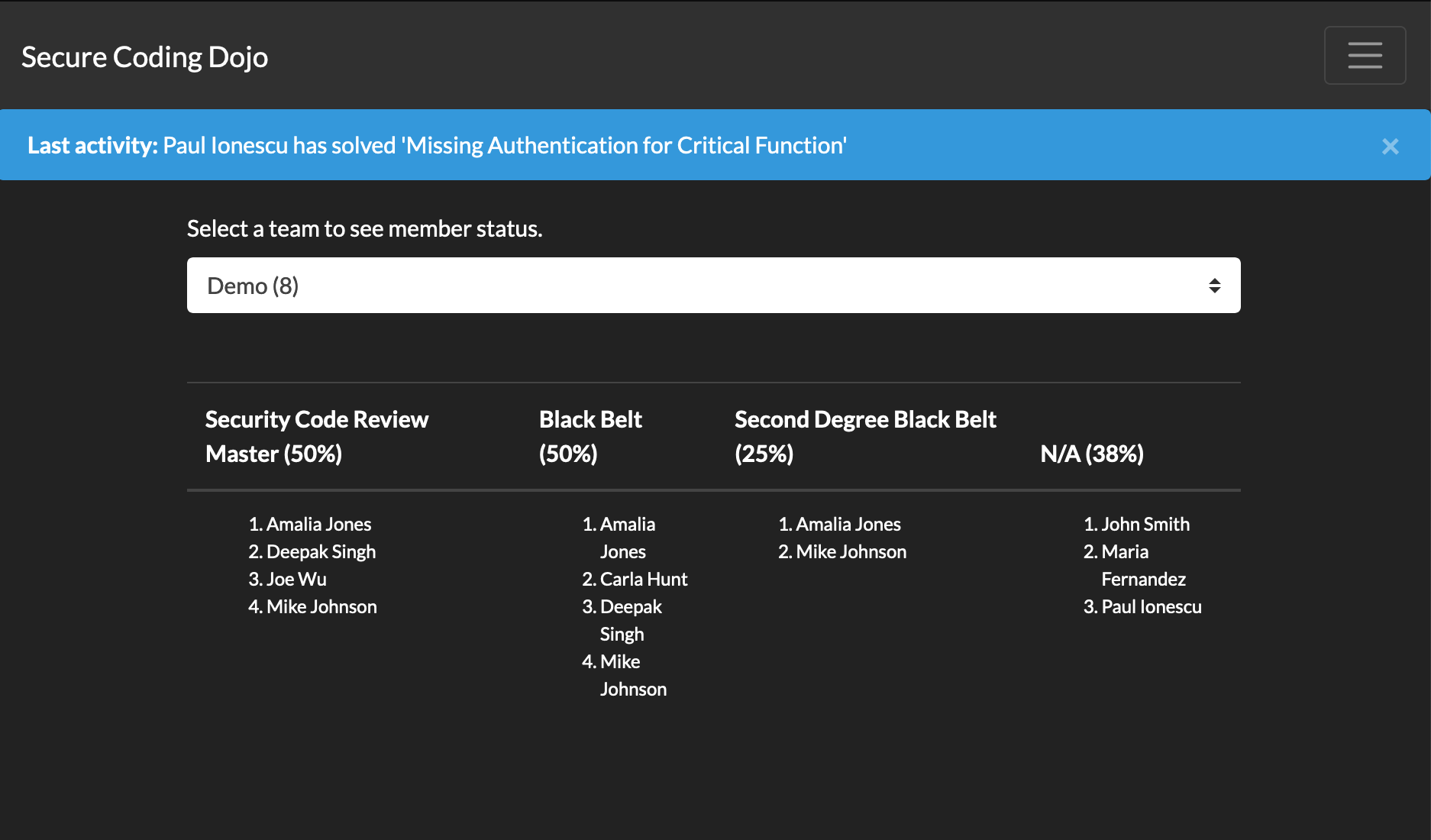
The page listing the participants and their corresponding levels